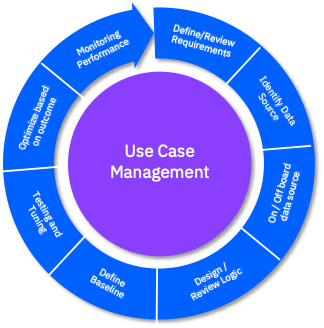
Use Case Model of the Enhanced, Evidence-Based Cyber Crime Prosecution... | Download Scientific Diagram
![PDF] A Use Case in Cybersecurity based in Blockchain to deal with the security and privacy of citizens and Smart Cities Cyberinfrastructures | Semantic Scholar PDF] A Use Case in Cybersecurity based in Blockchain to deal with the security and privacy of citizens and Smart Cities Cyberinfrastructures | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/894422818808260bae2c8bf6a63ea61deb52686c/3-Figure2-1.png)
PDF] A Use Case in Cybersecurity based in Blockchain to deal with the security and privacy of citizens and Smart Cities Cyberinfrastructures | Semantic Scholar